Feature
No tools by default. You grant exactly what's needed.
Per-agent, per-directory access control that goes beyond what OpenClaw alone provides.
Most platforms start with "everything allowed" and ask you to block what's dangerous. That's backwards for AI agents that can read files and execute commands.
Pinchy starts with nothing allowed. A newly created agent is a blank slate — it can chat, but it can't access any tools, files, or external resources until you explicitly enable them.
"Allow everything, block the dangerous stuff."
Problem: You have to anticipate every risk. Miss one tool, miss one directory, and the agent has access you didn't intend.
"Block everything, enable what's needed."
Benefit: The worst case is an agent that can't do something. You add permissions as needed. No surprises.
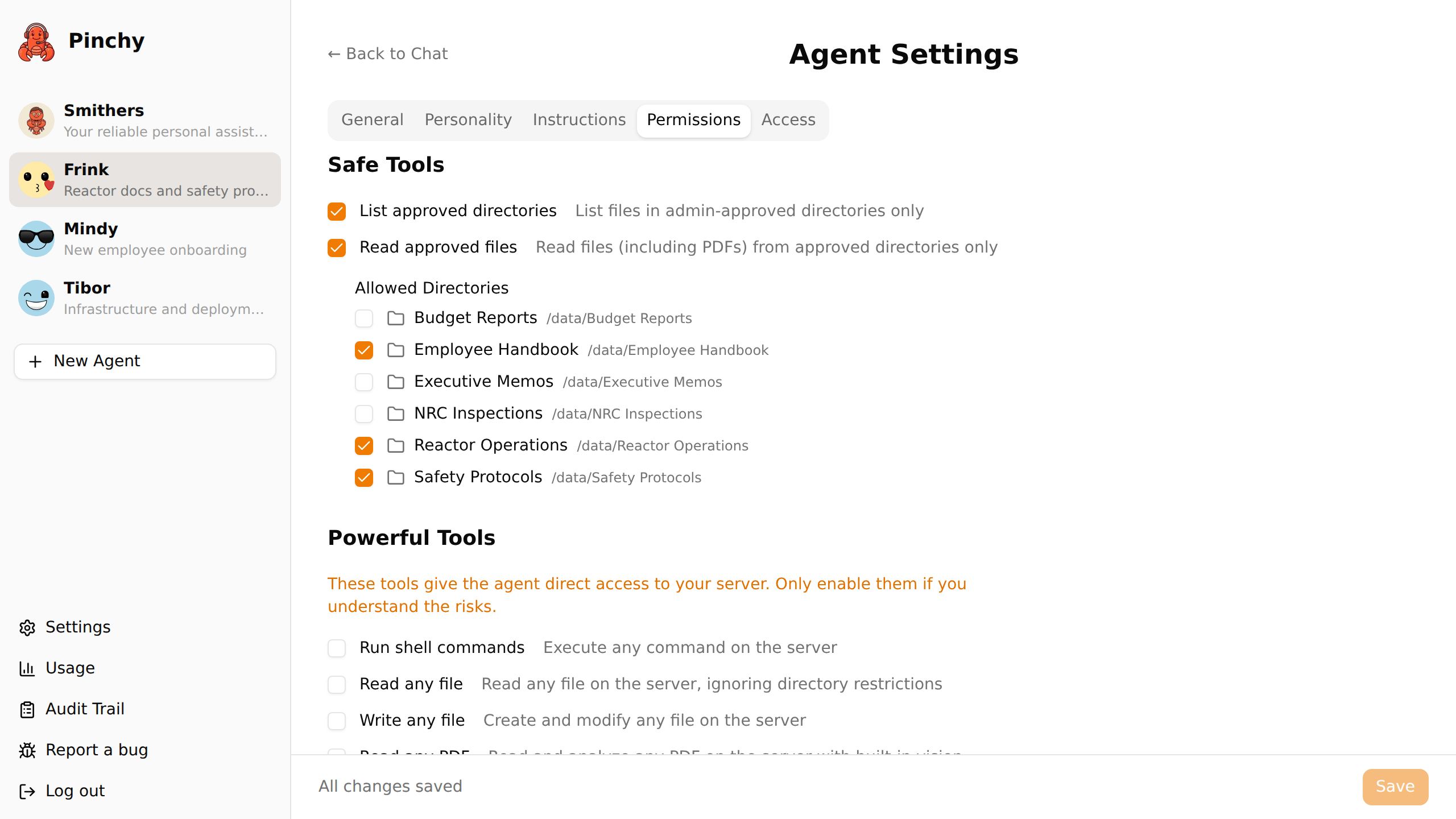
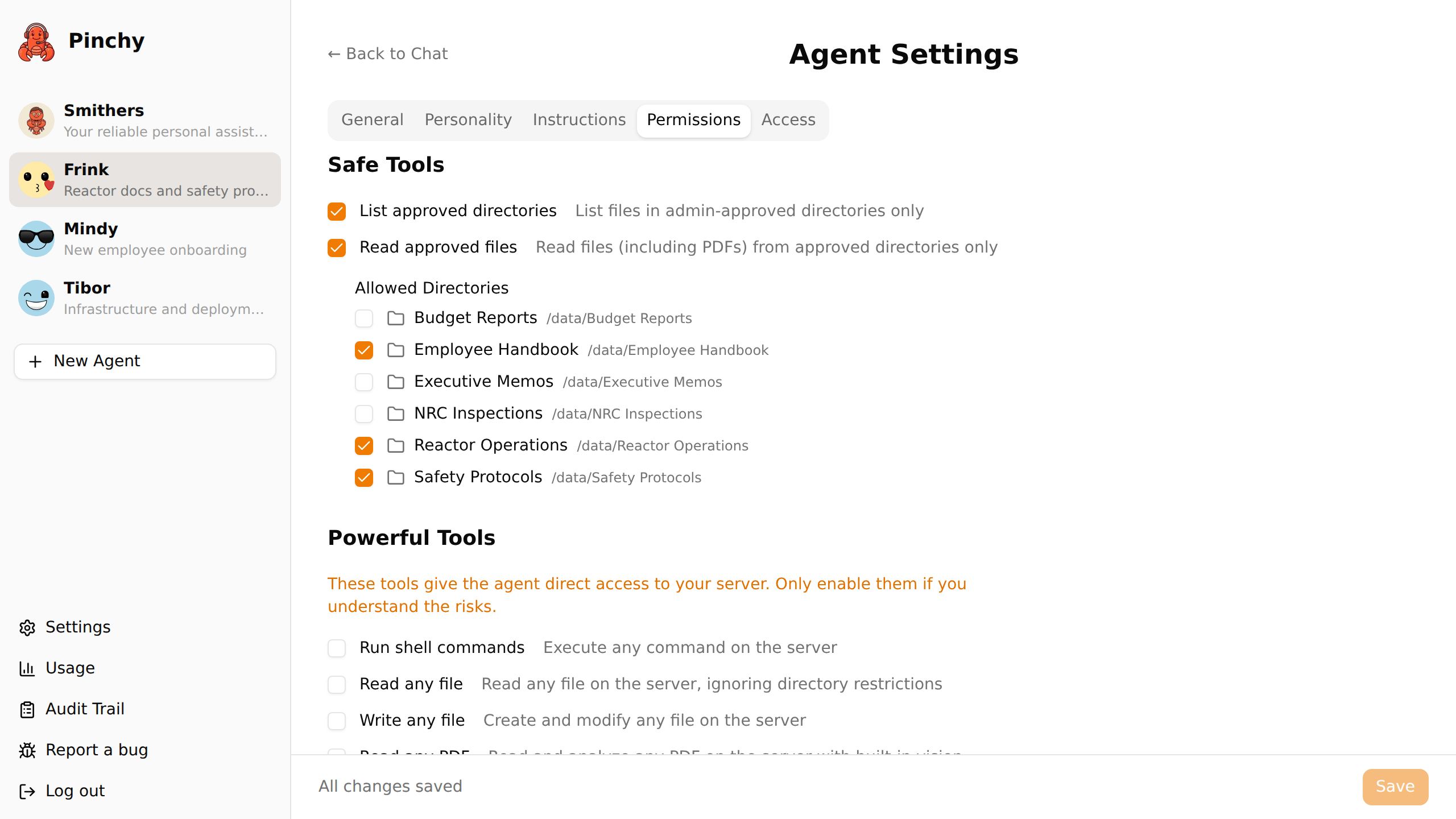
Pinchy organizes tools into two categories based on their risk profile:
Sandboxed access to admin-approved directories. The agent can list and read files — but only in directories you've selected. Every file access request is validated at runtime against the approved paths.
Full capabilities that require more trust. Shell execution, web browsing, unrestricted file access. Enable these only for agents that genuinely need them, operated by users you trust.
This is the feature that makes Pinchy's permissions fundamentally different from OpenClaw's built-in tool configuration.
OpenClaw lets you say: "This agent can read files." Pinchy lets you say: "This agent can read files only in /data/hr/ and /data/policies/."
The directory picker is visual — no path guessing, no config files. Select directories, save, done. The validation happens at runtime, not just at configuration time.
Agent permissions control what data an agent can access. Groups control who can talk to the agent. Together, they create real data isolation:
| Agent | Can access | Available to |
|---|---|---|
| HR Assistant | /data/hr/, /data/policies/ | HR Group only |
| Finance Agent | /data/finance/, /data/reports/ | Finance Group only |
| Company Wiki | /data/wiki/ | Everyone |
The finance team can't even see the HR agent. And even if they could, the HR agent can't access finance data. Two independent layers.
30-minute demo. We'll set up an agent with scoped permissions and show you how data isolation works in practice.