Feature
Every agent action, cryptographically signed and permanently recorded.
Your compliance team can trace exactly what happened, when, and who triggered it.
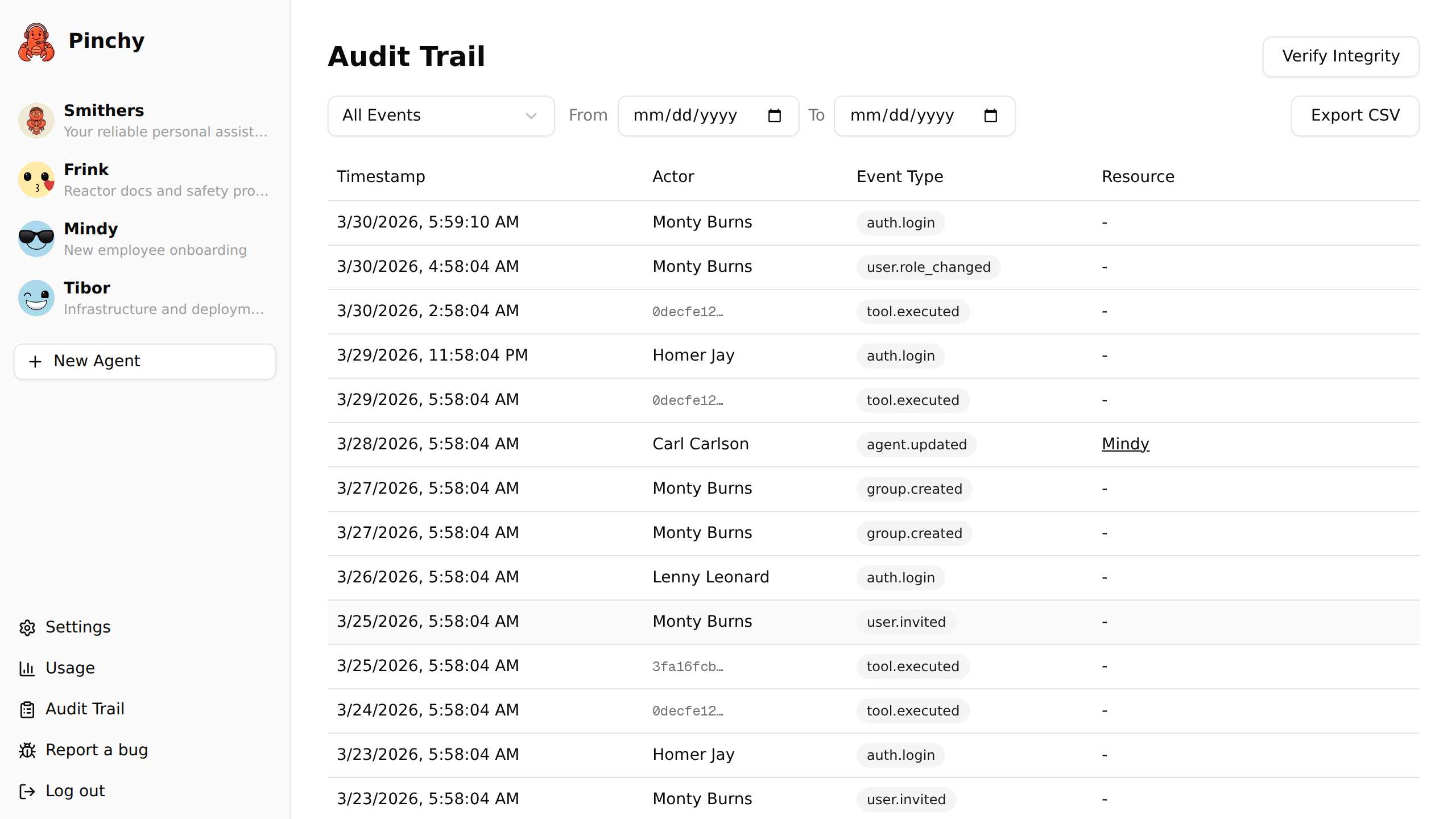
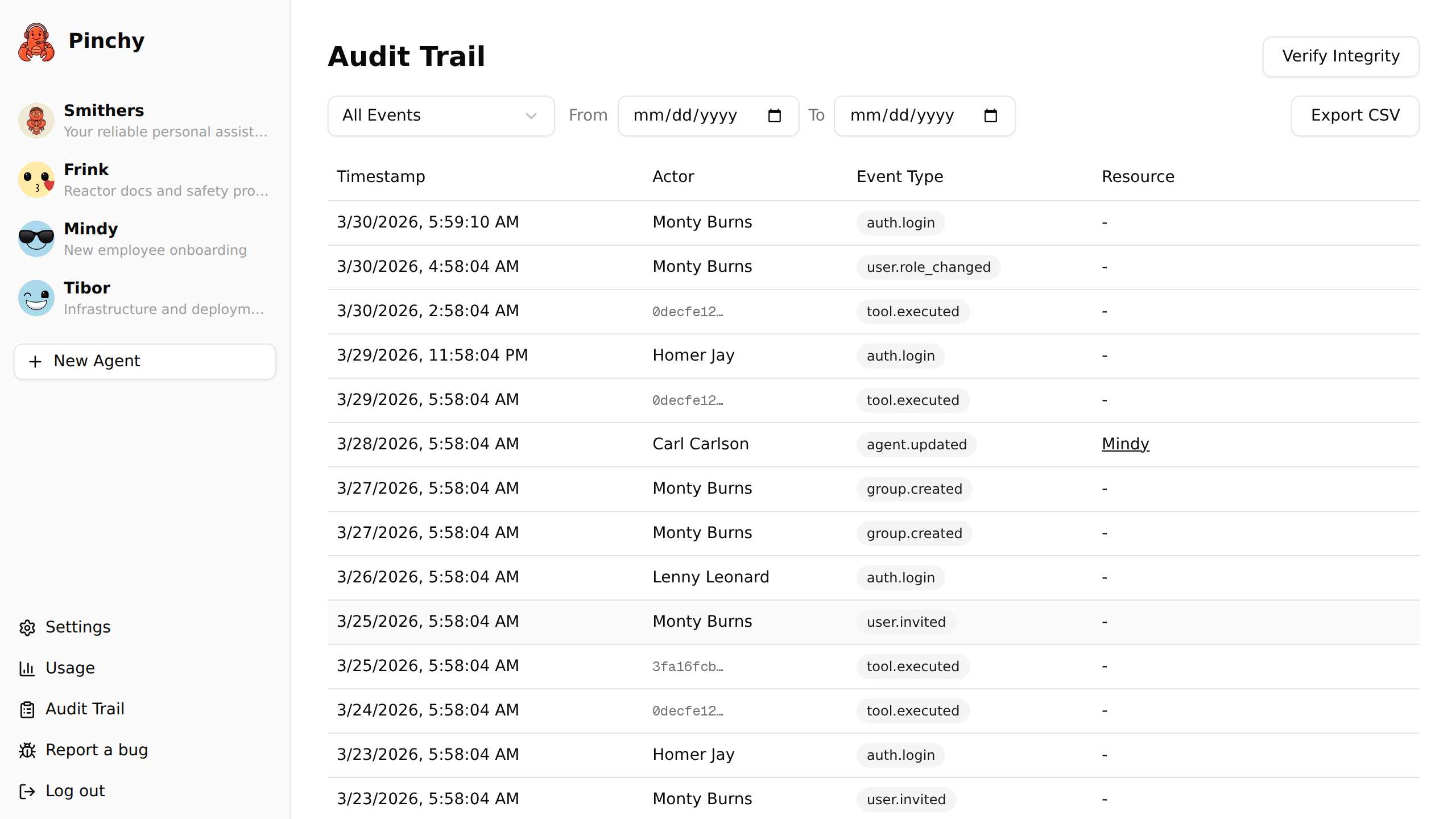
Pinchy logs events across six categories. Every entry includes a timestamp, the actor (user or system), and a cryptographic signature.
Every tool an agent uses: file reads, shell commands, web requests. The log includes the tool name, parameters, and result. If an agent tries to use a tool that's not in its allow-list, that gets logged too.
Successful logins, failed attempts, password resets. You see who accessed the platform and when. Failed login attempts are logged with the attempted email for security monitoring.
Agent created, updated, deleted. Personality changes, permission changes, tool configuration changes. The full before-and-after state is captured.
Invitations sent, accounts created, roles changed, users deactivated. Every change to who can access the platform is recorded.
Provider settings, enterprise key changes, context updates. When an admin changes platform-wide settings, the audit trail captures it.
Group created, members added or removed, agent visibility changed. The full history of who had access to what, and when it changed.
Audit logs are only useful if you can trust them. Pinchy uses three mechanisms to ensure integrity:
Every audit entry is signed with a server-side secret. The signature covers the event type, actor, timestamp, and details. Modifying any field invalidates the signature.
PostgreSQL triggers prevent UPDATE and DELETE operations on audit entries. The only allowed operation is INSERT. Even a database admin running raw SQL triggers the protection.
The built-in verifier recomputes every row's signature against the server-side secret and returns the IDs of any row whose signature no longer matches. One click, entire log checked, bad rows flagged.
Honest note: This is tamper-evident, not tamper-proof. Someone with direct database access and the signing secret could re-sign a modified row. But they can't do it silently — any external backup, SIEM export, or previously exported CSV would reveal the discrepancy. For most compliance scenarios, tamper-evidence is exactly what auditors need.
See only tool executions, only auth events, only agent changes. The event type filter narrows the view to exactly what you're investigating.
What did a specific user trigger? What did a specific agent do? Actor-based filtering for incident investigation and user activity reviews.
Export the full audit trail as CSV, including every row's HMAC-SHA256 signature. Feed it into your SIEM, archive it, or run independent verification.
AI agents can read files, execute commands, and access sensitive data. Without an audit trail, you're trusting that nothing went wrong. With an audit trail, you can prove it.
ISO 27001, SOC 2, GDPR Article 30 — they all require records of data processing activities. The audit trail provides them automatically.
Something unexpected happened? Trace the exact sequence of agent actions, tool calls, and data accessed. Minute-by-minute reconstruction.
Your team trusts AI agents more when they know every action is logged. Transparency reduces resistance to adoption.
30-minute demo. We'll show you the full audit trail, verification tool, and how it integrates with your compliance workflow.